Each year, Datto, a global provider of security and cloud-based software solutions, surveys 1,000 Managed Service Providers (MSPs) on the state of ransomware from the perspective of the IT channel and the small and medium business (SMB) clients it serves. We’ve compiled some of the key takeaways from the Global State of the Channel Ransomware Report and interpreted what it might mean for your organization.
What is Top-of-Mind for IT Experts
Though the cybersecurity landscape has moved to the forefront of what is top-of-mind for company leads, the types of cybersecurity threats remain similar to previous years
- 70% of MSPs report that ransomware is still the number one malware threat.
- Phishing is still a cybercriminal’s most successful way into an SMB due to weak passwords, poor security practices, and lack of general cybersecurity education.
Digging into the leading causes of successful ransomware attacks reveals that Phishing attempts exceed all other vulnerabilities cited by survey respondents. Phishing as most of us know it, occurs in email, but there has been an uptick in SMS or text message-based phishing, called smishing.
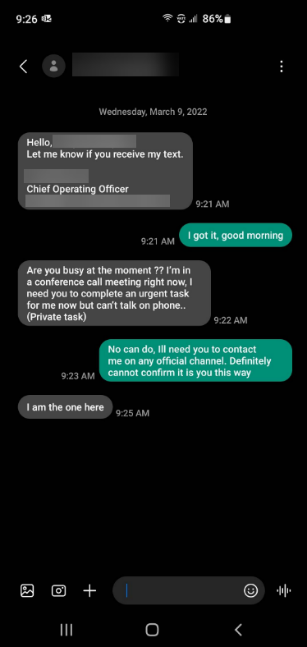
Bad actors look to create a sense of urgency by posing as high-ranking company executives in a text message. They then pressure the target to provide them with company information or grant them access to the company network. Figure 1 is an example of a real-life smishing attempt. In this instance, the end-user was suspicious and did not fall victim to the cyber-attack.
End-User education is essential for front-line ransomware protection. Security training must help end-users identify and shut down phishing/smishing attacks. Our clients use KnowBe4 to provide regularly scheduled training and weekly updates are sent to their inboxes.
Impact of an Attack
Training is just the first step and often isn’t enough on its own. According to Datto, organizations report that even if an attack is resolved quickly, the aftermath can be devastating.
- 62% of MSPs said clients’ productivity was impacted and 39% said clients experienced business-threatening downtime.
- Average cost of downtime in 2020 was nearly $275,000, 94% higher than reported in 2019.
- 91% of MSPs report clients with Business Continuity and Data Recovery solutions in place are less likely to experience significant downtime during a ransomware attack.
The impact of downtime can be significant. Malware left undetected can impact numerous devices, servers, and even data. Restores can be time-consuming, especially when using traditional backup tools. Ransomware recovery efforts can take an MSP over 200 hours to complete. Oftentimes, organizations experience a complete work stoppage during those efforts.
When it comes to ransomware attacks, MSPs report the cost of downtime – lost business plus recovery efforts charged as time and materials – can be nearly 50x greater than the ransom requested.
What Can You Do?
It is important for organizations that fall victim to a ransomware attack to identify the attack, shut it down and restore business operations as quickly as possible. One tool helping cybersecurity experts accomplish this is Endpoint Detection and Response technology. Behavioral-based detection technology identifies threats more proactively and solutions like SentinelOne Complete® have the built-in ability to roll machines back to a pre-infected state. Learn more about EDR solutions here.
NPR reported last year that there are seven ransomware attacks every hour in the United States. And, according to Datto’s survey, 92% of surveyed MSPs predict ransomware attacks will continue at current, or worse, rates. These statistics have motivated many organizations to operate with a “not if, but when,” mentality when it comes to the potential for an attack. It’s important to prepare your entire organization to protect your people, data, and business.
Our cybersecurity services team’s purpose is to protect and prepare our clients for an attack. If you’d like to learn more about how our IT experts could help protect your organization, contact us at security@gadellnet.com.