Digital assets form the backbone of modern organizations. Without a clear picture of your IT vulnerabilities, you’re operating blind. IT risk assessments serve exactly this purpose: they identify and mitigate potential vulnerabilities before they can be exploited.
As organizations increasingly rely on interconnected technologies, cybersecurity strategies are no longer optional. An IT risk assessment or security vulnerability analysis is the foundation—a structured approach to understanding and managing potential risks to your data, your people, and your organization.
This guide covers the significance of IT risk assessment and its role in cybersecurity. You’ll learn the key components of a risk assessment, understand the benefits of completing one, and review current trends shaping the process.
The goal is straightforward: We want you to understand why IT risk assessments matter and how to use them to strengthen your security.
What You Need to Know About IT Risk Assessment
IT risk assessment is a systematic process that evaluates potential threats and vulnerabilities within your organization’s IT infrastructure. It answers a basic question: what could go wrong, and what’s the impact if it does?
The assessment process has three parts: identify threats to your systems, evaluate the vulnerabilities that could be exploited, and estimate the potential impact. This structured examination helps you prioritize where to focus and where to implement security measures to mitigate identified risks.
Most organizations use an IT Risk Assessment Template to ensure completeness. A template provides a framework for a technology-focused audit of systems and processes, ensuring nothing gets missed.

An IT risk assessment is the first step in broader risk management. You use the knowledge gained to allocate resources, minimize risk impact, and control exposure. This foundation lets you navigate the threat landscape effectively.
After completing a thorough risk assessment, you’re prepared to move forward on your strategic technology roadmap. Leaders make decisions about cyber liability insurance, mobile device management, and cloud versus on-premises infrastructure from a position of actual knowledge, not assumption.
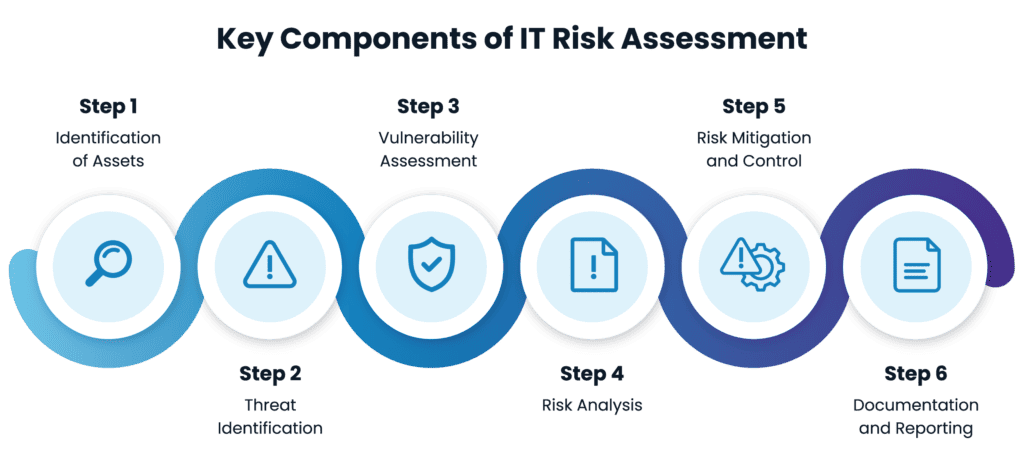
What Are the Key Components of IT Risk Assessment?
Most IT Risk Assessments have commonalities using a standard operating procedure to efficiently move through all major components. Remember, some vulnerabilities may be small and feel insignificant. Moving through an evaluation process systemically will ensure your organization isn’t missing a small vulnerability that could lead to a large issue. Many assessments involve four major components—identification, evaluation, analysis, and results reporting. Each component can have multiple layers as outlined below.
Identification of Assets: Involves cataloging and understanding the organization’s technology assets, including hardware, software, data, and intellectual property. Not only will this process aid in risk assessment, but it also aids your organization in evaluating its current technology investments. It is a valuable tool not only for risk assessment but for creating a technology strategic roadmap.
Threat Identification: Encompasses the identification of potential threats that could exploit vulnerabilities in the organization’s IT systems. This component helps in understanding the landscape of potential risks that are unique to your organization. A risk assessment template aids in evaluating the types of threats that your organization is most likely to encounter.
Vulnerability Assessment: Focuses on evaluating the weaknesses and vulnerabilities within the organization’s IT infrastructure. This step is crucial for understanding the potential entry points for threats. Cybersecurity infrastructure has three pillars to consider – people, process, and platform. A security vulnerability assessment helps you evaluate each pillar individually so you can determine where improvements may need to be made.
Risk Analysis: Involves the evaluation of the identified threats, vulnerabilities, and the potential impact of a security incident. This analysis helps the organization see all the potential risks and then aids in prioritizing those risks based on their severity.
Risk Mitigation and Control: Encompasses the development and implementation of strategies to mitigate or control the identified risks. This includes the establishment of security controls and measures to reduce the likelihood and impact of potential incidents. Using an assessment template also aids in prioritizing the measures the organization will take and creating a timeline so the organization can move swiftly yet responsibly.
Documentation and Reporting: Involves the documentation of the entire risk assessment process and the preparation of comprehensive reports. This component aids in communication, decision-making, and ongoing risk management. This step also sets the foundation for assessing potential risks to these assets and provides thorough documentation. Complete documentation is important and will be used for efficient planning, effective threat response, and ongoing compliance support.
Benefits of IT Risk Assessment
There are many important benefits to completing an IT risk assessment. Most, if not more, would have an impact on your organization’s planning and overall security posture.
Identifying and Mitigating Risks Proactively: Conducting periodic IT risk assessments allows organizations to identify and mitigate potential threats and vulnerabilities before incidents occur. The assessment helps an organization better understand the risk landscape and therefore, they can implement safeguards, improvements, and other measures to enhance their cybersecurity posture.
Contributing to Proactive Cybersecurity Measures: Not only will an IT risk assessment help an organization identify potential risks but learning about potential vulnerabilities can contribute significantly to the development of ongoing proactive cybersecurity measures. By identifying and addressing risks before they materialize into security incidents, organizations can stay ahead of potential threats, protecting their digital assets effectively.
Improved Incident Response Preparedness: By understanding potential risks and vulnerabilities, organizations can enhance their incident response preparedness. IT vulnerability assessments provide a roadmap for responding to security incidents effectively, minimizing the impact and downtime associated with breaches.
Enhancing Business Continuity Planning: IT risk assessments play a crucial role in responding to an event but also in crafting a business continuity plan. By identifying and mitigating potential risks to people, platforms, and processes, organizations ensure the resilience of their operations, minimizing disruptions and ensuring continuity even in the face of unforeseen events. A business continuity plan built with assessment results in mind allows each of your organization’s leaders to react quickly and cohesively to a business interruption.
Meeting Regulatory Compliance Requirements: Risk assessments are instrumental in meeting regulatory compliance requirements. Many regulatory frameworks, such as GDPR and HIPAA, mandate organizations to assess and manage risks to safeguard sensitive information. Compliance with these regulations is crucial for avoiding legal repercussions and maintaining trust.
In addition, many cyber liability insurance plans have many requirements to be met before coverage can be provided. An IT security vulnerability analysis, though not necessarily mandatory, can make the renewal process more efficient.
Enhanced Decision-Making: The insights gained from IT risk assessments empower organizations with data-driven decision-making. Leaders can make informed choices regarding resource allocation, security investments, and strategic planning to address potential risks effectively.

What Makes an IT Risk Assessment Effective?
An effective IT risk assessment follows a systematic process: identify and catalog digital assets, analyze potential threats and vulnerabilities, evaluate likelihood and impact, prioritize risks by severity, develop mitigation strategies, and regularly review and update findings.
Two main methodologies guide this work:
Quantitative Assessment assigns numerical values to risks, producing objective measures of potential impact. However, quantitative assessment requires access to curated data. If you lack historical breach data or incident records, this approach is difficult.
Qualitative Assessment uses descriptive terms to assess risks. It works quickly and can be applied to most business functions. The tradeoff: qualitative analysis can be biased or limited by the experience of those conducting it.
Most organizations use a combined approach, leveraging the strengths of both for thorough and efficient results. Understanding both methodologies lets you choose what works best for your situation.
Collaborative risk evaluation matters. Engage stakeholders from IT, legal, compliance, and business units. Different departments see different risks. This diversity ensures a more comprehensive and accurate assessment.
Leverage specialized risk assessment tools and software to streamline the process. These tools often include asset identification, risk analysis, and reporting features. Technology can enhance efficiency and accuracy.
IT security audits complement risk assessments. Audits examine your security controls and practices, verify the effectiveness of existing measures, and identify improvement areas. They validate the accuracy of risk assessments and ensure controls align with industry best practices.
Risk assessment is not a one-time event. The threat landscape changes constantly. Organizations must regularly reassess and adapt findings to stay ahead of emerging risks. This involves periodic reviews, updates, and ongoing stakeholder collaboration.

Trends in IT Risk Assessment
Focus on Cloud Security Risks: With the widespread adoption of cloud services, there is a growing emphasis on assessing and managing risks associated with cloud environments. IT risk assessments are evolving to address unique challenges related to cloud security, such as data protection, identity management, and shared responsibility models.
Quantification of Cyber Risk: There is a trend towards quantifying cyber risk in financial terms. Organizations are seeking to express cybersecurity risks in monetary value, enabling better communication with business stakeholders. This approach facilitates informed decision-making regarding risk mitigation investments like right-sizing cyber liability coverage.
Regulatory Compliance Evolution: As regulatory frameworks evolve, there is an increasing focus on incorporating regulatory compliance requirements into IT risk assessments. Organizations are aligning risk assessment processes with the changing regulatory landscape to ensure continuous compliance and reduce legal and financial risks.
Enhanced Automation in Risk Assessment Processes: Automation is becoming more prevalent in conducting risk assessments. Automated tools can streamline data collection, analysis, and reporting, allowing organizations to perform more frequent risk assessments. This trend is expected to improve efficiency and ensure assessments are conducted in near real-time.
To further enhance the accuracy and speed of risk assessments, organizations are increasingly using the integration of AI-driven (Artificial Intelligence) tools to analyze vast amounts of data, identify patterns, and predict potential risks more efficiently than traditional methods.
Advanced Threat Intelligence: IT risk assessments are increasingly leveraging advanced threat intelligence sources. Continuous monitoring of global threat landscapes and understanding the tactics, techniques, and procedures employed by cyber adversaries provide organizations with real-time insights to enhance their risk assessment strategies.
Securing Your Organization Starts with Assessment
IT risk assessments play a critical role in identifying vulnerabilities and mitigating threats. They’re not a compliance checkbox—they’re a foundation for security strategy and business continuity.
A thorough assessment delivers concrete benefits: proactive risk mitigation, better incident response, improved business continuity, regulatory compliance, and informed decision-making. IT risk assessments are increasingly important to strategic technology planning. Emerging trends—cloud security, compliance requirements, and AI-driven automation—make assessments essential for security and productivity.
IT risk assessments empower organizations to operate with confidence, understanding their actual risk exposure and how to address it.
Frequently Asked Questions
What is an IT risk assessment?
An IT risk assessment is a systematic evaluation of potential threats and vulnerabilities in your organization’s IT infrastructure. It identifies what could go wrong, evaluates the likelihood and impact, and recommends mitigation strategies.
How often should an organization perform an IT risk assessment?
Most organizations should perform a comprehensive risk assessment annually. However, you should conduct targeted reassessments whenever significant changes occur: new systems, personnel changes, regulatory updates, or after security incidents. Many also perform quarterly reviews of high-risk areas.
What is the difference between a risk assessment and a security audit?
A risk assessment identifies potential threats and vulnerabilities and prioritizes them by severity. A security audit examines existing security controls and verifies they’re working as intended. Audits validate risk assessment findings and ensure controls meet best practices. They complement each other.
What does an IT risk assessment template include?
A good template includes sections for asset identification, threat identification, vulnerability assessment, risk analysis, mitigation strategies, and documentation. It provides a structured framework to ensure completeness and consistency across assessments.
Does my organization need an IT risk assessment to qualify for cyber liability insurance?
Not always mandatory, but many cyber liability insurance plans require or strongly prefer documented risk assessments. At minimum, a completed assessment streamlines the insurance application and renewal process. It also helps you understand your actual coverage needs based on your real risk profile.
